SOC 2 Compliance & Certification Support
- ITIO Innovex helps organizations implement strong security controls and prepare for SOC 2 compliance and audit readiness.
- SOC 2 is an internationally recognized framework developed by the American Institute of Certified Public Accountants (AICPA). It helps companies protect customer data and maintain secure systems.
- Many global companies require SOC 2 compliance before working with technology vendors, SaaS providers, and cloud service companies.
What is SOC 2?
SOC 2 (System and Organization Controls) is a security and compliance framework used to evaluate how an organization protects customer data.
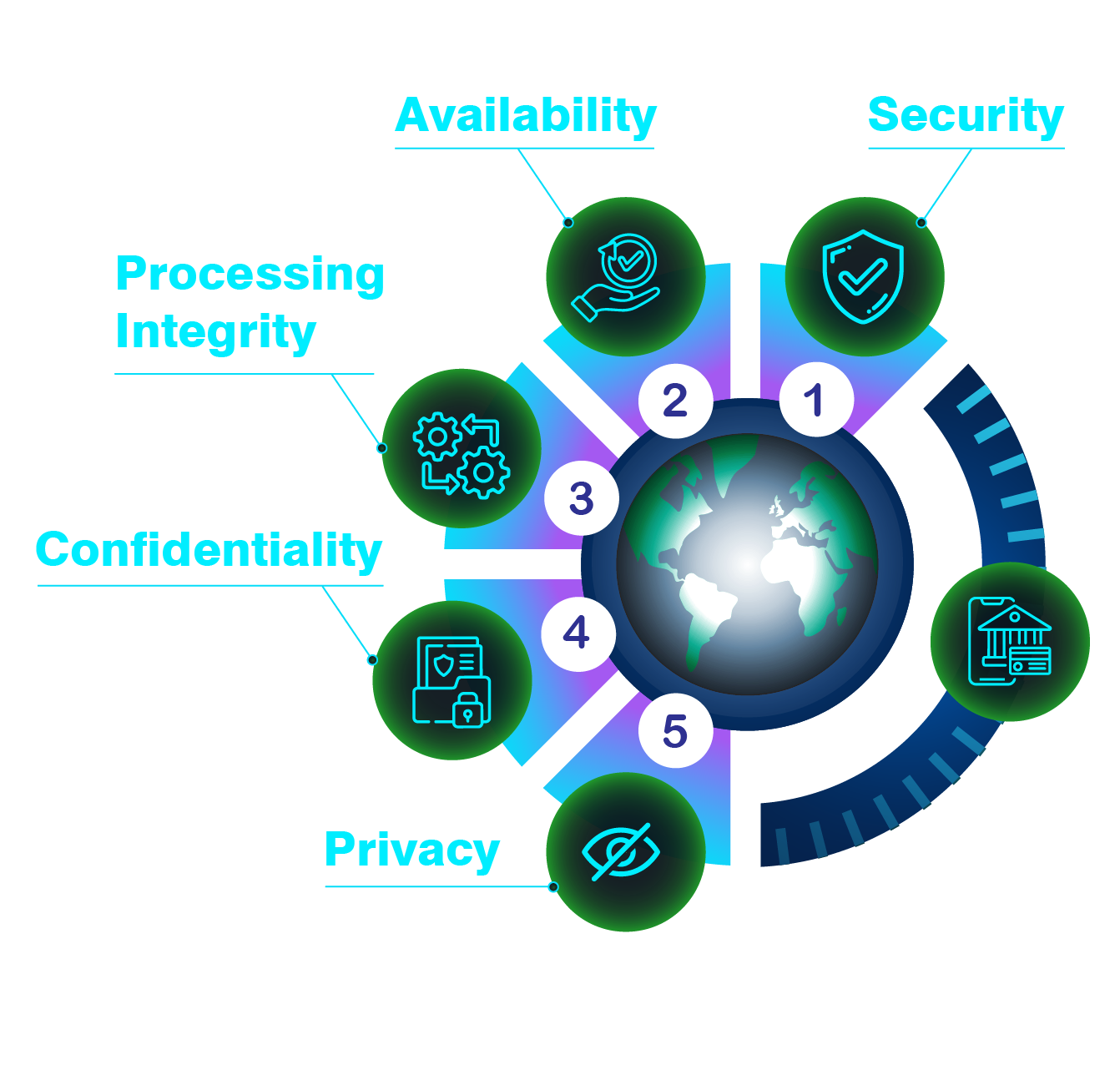
SOC 2 focuses on the following five security principles:
Security
Availability
Processing Integrity
Confidentiality
Privacy
Organizations that store or process sensitive customer data must implement strong security controls based on these principles.
SOC 2 compliance helps organizations:
Build trust with customers and partners
Demonstrate strong security practices
Protect sensitive customer information
Reduce cybersecurity risks
Meet vendor and enterprise security requirements
Gain competitive advantage in global markets
SOC 2 Report Types
SOC 2 Type I
SOC 2 Type I evaluates whether the required security controls are properly designed and implemented at a specific point in time. This report confirms that the organization has the necessary policies, procedures, and controls in place.
SOC 2 Type II
SOC 2 Type II evaluates how effectively these security controls operate over a period of time, usually between 3 to 12 months. This report provides stronger assurance that the organization consistently maintains its security controls.
Our SOC 2 Services
SOC 2 Readiness Assessment
Evaluate the current security posture of your organization and determine readiness for SOC 2.
Gap Analysis
Identify gaps between existing processes and SOC 2 requirements.
Security Policy Development
Create and implement security policies, procedures, and governance frameworks required for SOC 2.
Risk Assessment
Identify potential security risks and implement proper controls to protect systems and data.
Documentation & Evidence Preparation
Prepare necessary documentation and evidence required for SOC 2 audit.
Audit Preparation Support
Assist organizations in preparing for the SOC 2 audit conducted by independent CPA auditors.
Who Needs SOC 2?
SOC 2 compliance is recommended for organizations such as:
SaaS companies
Cloud service providers
Fintech companies
IT service providers
Data processing companies
Technology startups handling customer data
Benefits of SOC 2 Compliance
SOC 2 compliance provides several benefits for organizations that manage sensitive customer data.
Builds trust with enterprise customers
Improves security governance and risk management
Strengthens protection of sensitive data
Helps meet international security requirements
Supports business growth and partnerships
Unlock the Power of Seamless Payments with Our Payment Gateway Software
Provide your clients with a top-tier, customizable payment gateway. Integrate our solution under your brand or leverage the source code for full control.
Frequently Asked Questions
SOC 2 (System and Organization Controls) is a security compliance framework developed by the American Institute of Certified Public Accountants (AICPA). It helps organizations demonstrate that they have proper controls in place to protect customer data and maintain secure systems.
SOC 2 is commonly required for organizations that store or process customer data, such as SaaS companies, cloud service providers, fintech companies, IT service providers, and technology startups.
SOC 2 is based on five Trust Service Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
SOC 2 Type I evaluates whether security controls are properly designed at a specific point in time, while SOC 2 Type II evaluates the effectiveness of these controls over a defined period (usually 3 to 12 months).
The time required depends on the organization's size and existing security controls. SOC 2 Type I usually takes a few months, while SOC 2 Type II requires additional monitoring time.
SOC 2 audits are conducted by independent CPA audit firms.
A SOC 2 report is generally valid for 12 months.
ITIO Innovex provides SOC 2 readiness assessment, gap analysis, security policy implementation, documentation support, and audit preparation to help organizations achieve SOC 2 compliance.
Our Partners






